Information Technology (IT) teams are tasked with the unenviable job of protecting the enterprise network infrastructure. Every year presents new challenges as cybercriminals constantly change their tactics and more sophisticated malware tools hit the market. Deceit in the form of cybercrime is now a multibillion-dollar industry and we’re all targets.
IT experts work hard to stay ahead of cybercriminals by enabling multiple layers of security service. In order to minimize the impact on business productivity, these tools are not as invasive or limiting as they should be to stop all the malware. With minimally disruptive settings for security tools, IT experts are finding that the criminal element is discovering new and creative ways around these defences.
To further mitigate malware risks, organizations are turning to their next line of defence—their employees.
By providing security awareness training, these companies are establishing their Human Firewall. This defence structure is integral to securing the company.
This new form of training provides insight into the techniques used by cybercriminals to perform their illicit activities and shows employees how to avoid traps. The Human Firewall is important for both physical (e.g., someone trying to get into a secured area) and digital (e.g., malware) defence.
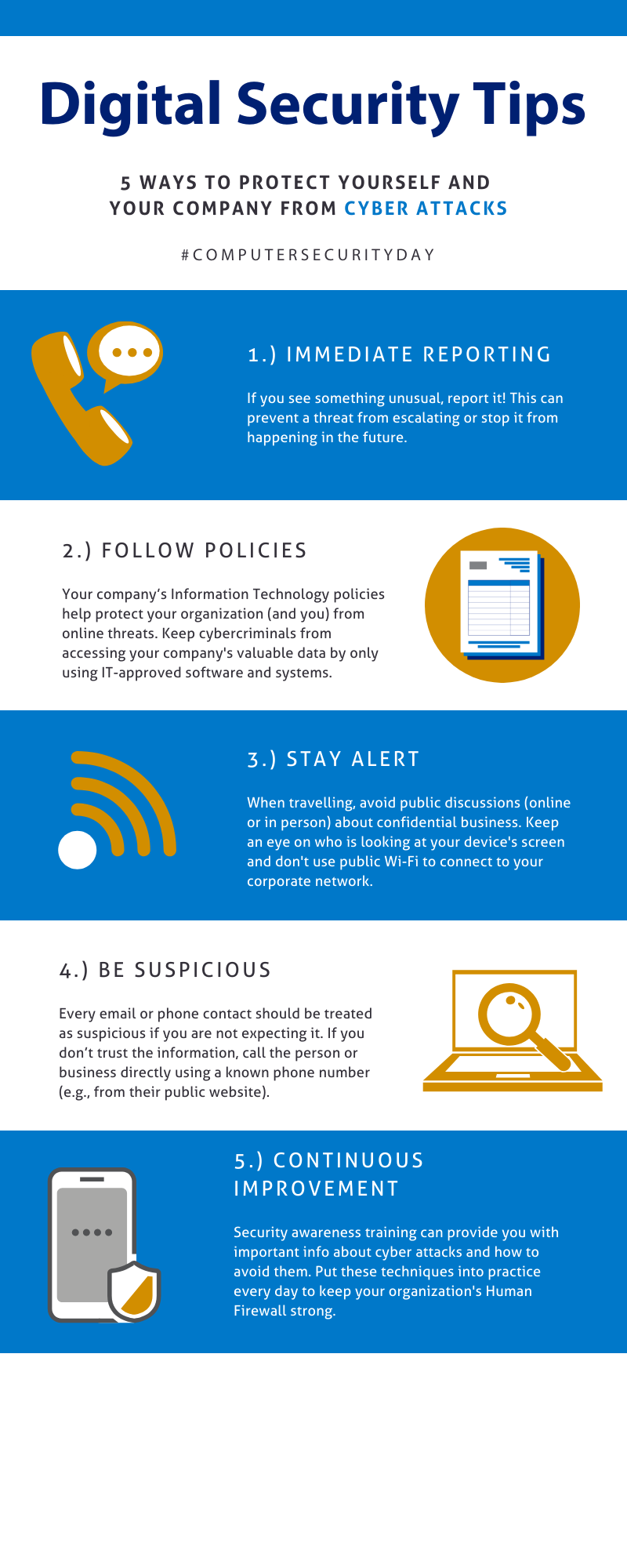
Here are five ways employees can keep their companies safe from digital threats. See the infographic at the end of this post for a quick overview.
Immediate Reporting
If you see something out of the ordinary or receive something suspicious (e.g., a change in bank information from a vendor), report it as soon as possible to help prevent an active threat or future issues. Regardless of the nature or complexity of what you experienced, it’s safer to report it and have the incident investigated (even if it turns out to be nothing) than to ignore it and have someone else fall victim.
Follow Policies
Your company’s IT policies help protect your organization (and you) from online threats. They might seem annoying or overly cautious but know that they are there for a good reason, even if it doesn’t seem obvious at first.
Always follow your organization’s policies, and as tempting as it might be, don’t develop workarounds. Policies are established to support the level of acceptable risk for a business. Failure to follow these policies could put your organization at a high level of risk and cost. An example of this is shadow-IT where systems and services are setup by non-IT employees that ignore standards and guidelines established by the business.
Stay Alert
Be consciously aware of what is normal or acceptable in your business’s operations. Talk to your co-workers about unusual things you experience while online—whether at work or at home. Anything out of the ordinary should be acknowledged and investigated/addressed.
When travelling, make sure to avoid public discussions regarding confidential business—online and in person—and watch for people trying to read documents off your device’s screen. When logging onto your corporate network in a public place, ensure you protect your login information and avoid public Wi-Fi. All these incidents could lead to a security breach at your organization.
Be Suspicious
Treat every new email as an “unknown” until you can determine they are from a known contact or entity. Check the time it was sent; if it was sent during non-business hours, be careful. Watch out for links sent in emails. Always hover over them to make sure the link is taking you to where you expect.
Every email or phone contact should be treated as suspicious if you are not expecting it. If you don’t trust the information, then call the person or business using a known phone number (not the one in the email or the one they give you as this could be a direct link to the criminal).
Continuous Improvement
An effective Human Firewall requires ongoing education to support proactive, habit-forming behaviour and to create awareness about new tactics and threats.
The new tips and techniques learned from security awareness training should be put into practice to effectively ward off criminals and their attempts to compromise security layers.
This post was written by former SRC employee, Chuck Ingerman.